Kiss Your Fitness Apps Goodbye, Motherf***ers
Love broadcasting your fitness routine to everyone and their mother? Bad news, you vain bastard: The Department of Defense is...
Love broadcasting your fitness routine to everyone and their mother? Bad news, you vain bastard: The Department of Defense is cracking down on service members' use of geolocation services out of concern for operational security, which means you can no longer digitally flex for your fellow warfighters and their spouses while downrange.
- According to an August 3 memo from Deputy Defense Secretary Patrick M. Shanahan released to the public on Monday, DoD personnel are hereby prohibited from “using geolocation features and functionality on both non-government and government-issued devices, applications, and services” while deployed to operational areas, including ships at sea.
- It's not just about using those features. As of right now, all devices with even the capability of geo-tagging troops’ locations are banned in operational areas, Army Maj. Audricia Harris, a Pentagon spokeswoman, told Task & Purpose: “If it is geo-location capable, you are prohibited from using that device.”
- Exemptions are available at the discretion of various combatant commanders “after conducting a threat-based comprehensive [OPSEC ] survey” and only based on “mission necessity,” which means you'll likely be barred from turning on any geolocation service unless your mission happens to include a fun run.
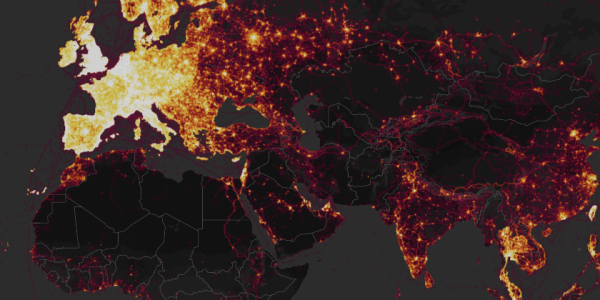
- In January, an online map published by consumer fitness data-gathering app Strava appeared to show the locations and behavior of U.S. military personnel deployed downrange. The following July, a joint investigation by Bellingcat and De Correspondent revealed that fitness app Polar was revealing life rhythms at sensitive locations, like intelligence agencies and nuclear weapons facilities, worldwide.
Will the new guidance change anything? Probably not: As Defense One pointed out following the Strave revelation, the Pentagon has long waged a losing war against the phenomenon of “data leakage,” the incidental and uncontrollable recording and dissemination of sensitive information in an age of ubiquitous mobile devices and wearable tech.
“The makers of such apps and services have vested interests in getting users to share as much data as possible: all companies scrutinize it to understand how people use their services; many also sell it to whomever will buy,” Defense One's Patrick Tucker wrote. “Most of the data is supposed to be anonymous, or run through a process called anonymization that strips it of personal info. But anonymization is hardly a foolproof concept. Consider the work of MIT data scientists César A. Hidalgo and Yves-Alexandre de Montjoye who showed in 2012 that four location data points were enough to de-anonymize an individual.”
OPSEC is important; broadcasting your run times is not. If you really need to show off, maybe just work on your Instagram game instead.
